Les inscriptions pour l’apéro géant #LittleFrenchtech du 23 Avril sont ouvertes ! https://t.co/jR92luLQoR #frenchtech pic.twitter.com/GqyOaA6Ncx
— LittleFrenchTech (@FrenchTechSuds) April 3, 2015
techno
W3C master plan for making the web a trusted place
Snowden has gone. Other privacy and or security stories happened. Some people might have forgotten but W3C does not and is still attempting to make the web more secure. Few pieces of technology reported here relates to that master plan.
W3C recommendation about Securing the Web is live.
That document named ‘Securing the Web’ is actually a finding from the stewards of the Web architecture, the W3C Technical Architecture Group, and deals with the usage of HTTPS. It basically says that it is preferable to actively use secure communication, to ease adoption of https:// and play with a trusted end-to-end TLS encryption on the Web (aka, do not use broken algorithms).
Web Crypto API is here (or almost).
The Web Crypto API has landed in several browsers, and it is under finalization. As soon as the testing activities will be completed and that two interoperable implementations will be evidenced, it will become an official W3C recommendation. In the meantime, you can still read Charles Engelke blog post [1] and table [2] tracking which browser implements which algorithm for which usage.
Spoiler : “RSA-PKCS1-v1_5 for digital signatures, RSA-OAEP for public key encryption, AES-CBC and AES-GCM for symmetric encryption, HMAC, and SHA-1 and SHA-2 hash functions are pretty much universally supported”
New WebAppSec guys mission, chosen.
The ones designing the web app security model are not legion, you can meet them in the W3C Web Security Working Group. If you want to know what they are willing to work on, you can have a look at their recently rechartered mission. Menu is impressive : garanteing web app silos, secure mashup, anti-clickjaking frames, user permission and HTTPS/HTTP juggling.
Security review will one day be natural.
There has been lots of discussions on the idea that W3C specification should actually go through a formal security revision. The main blocker from not implementing such a great idea is the lack of security experts, having enough time and money to perform an extensive and serious review. Mike West, from Google, started a security questionnaire that would help the editors and chairs of W3C groups to evaluate the sensitivity of the feature they are designing, and thus increasing awareness in the hole W3C community. The draft questionnaire is available here and anyone can contribute on the github project ! One should note that the W3C Privacy interest Group is also working on guidelines to help groups to reduce the fingerprint of the browser when designing their new features.
W3C TAG welcomed new security geeks.
Recent election in W3C Technical Architecture Group resulted in the addition of two skilled security members. Mark Nottingham from Akamai and Yan Zhu from Yahoo (yes, a girl in TAG, clap, clap, clap). This will definitely increase awareness of TAG on security best practices. Next challenge those two will face, is to clarify what are the types of resources in a browser that should only be accessed via a secure connection (aka Privileged Contexts).
All that good news will definitely favor the trust on the web.
And we should try to support it. As a reminder all W3C work is conducted in public and anyone is invited to bring their skills and share ideas. That is quite easy to do, as most of the working groups do have a public comment mailing list. Find the one you like and start contributing !
[1] http://blog.engelke.com/2015/03/
[2] https://docs.google.com/spreadsheets/d/14oTKnccypDRieszGLV7GbZXcIai0qLYOwgk_ELIj5A0/pubhtml
Note : picture by serge klk https://www.flickr.com/photos/sklkphoto/ under CC BY-NC-ND 2.0
Interview avec Stéph pour Duchess France
Dans mon parcours de girl in tech, j’ai rencontré des filles bien, des filles motivées, dont Stéphanie, developer evangelist chez Microsoft. Elle m’a récemment demandé d’expliquer en quoi consistait mon travail. Si vous avez envie de savoir ce que fait Virginie Galindo de ses journées, c’est par ici : http://www.duchess-france.org/interview-de-virginie-galindo-experte-securite-chez-gemalto-et-au-w3c/
FIDO Alliance : an amazing standardization story
As you know, my main job is to jump from one standardization body to another. In (my) history of meeting this kind of tribes, I have witnessed several birth and death of SDOs. I have gone to the traditionnal ETSI, the rich GSMA, the working hard GlobalPlatform, the always-been-here TCG, the fabulous W3C… None of them, from my view, had a development such as FIDO Alliance did. Seriously. Jumping from 4 founding folks (Lenovo, Validity, Paypal, NokNokLabs) to a list of 170 (paying) members in 2 years. This is amazing. For the ones who missed it, few facts and figures about FIDO Alliance.
FIDO Alliance primer goal is to design a solution for seamless authentication on the web, under user control. Born in 2013. Worked under the water during one year to write spec, evangelize and recruit. Showed at MWC 2014 – different products , including a commercial deployment by Samsung and Paypal. Announced a Google launch named Secure Key in October 2014. Issued its first set of specifications in December 2014 (aka 500 pages of architecture, protocol, documentation, …) and may surprise us again during the MWC 2015. In the meantime, the Board increased to 22 members, to include major players such as (sorry long but impressive list worth sharing it here) Alibaba, ARM, Bank of America, Discover, Google, Mastercard, Visa, Microsoft, NXP, Qualcomm, RSA and Samsung. Those guys are the ones paying the most and directing the strategy.
Seriously. So much people around that specific problem. There must be something. One may argue that at the moment the co-existence of two different technologies (UAF and U2F for acronyms geeks) may reduce the value of FIDO Alliance to solve one single problem. Maybe. But it kickstarted the market, and it was required to have Google family joining the conversation, and thus having all the major actors around the table.
Nevertheless, such growth should have never happened without the following assets :
– a clear value proposition : hey, come on, let’s kill passwords ! (a real challenge in the security area)
– a strong marketing and business development team, backed with serious financial interests, being everywhere, in any single conference approaching the authentication topic.
– a continuous positive and monitored communication, encouraging and valuing product or members PR.
– a clear governance : you pay, you decide, you pay less, you influence the technical stuff, you pay few, you listen and implement.
– good and committed technical folks to chair the working groups and edit the specs (folks like Brad Hill, Jeff Hodges, look at the names here).
– a pragmatic product functional compliance approach (aka interoperable test fest before thousands of tests being developed).
I’d say that FIDO Alliance may succeed or not (I wish it will), but the growth of that SDO is amazing and we should, first get inspiration from their good practices, and second, listen to FIDO Alliance announcement during this year, hoping those guys will talk loud.
Note : picture by abac077 “CC BY-NC-SA 2.0
Innovation et French Tech : une belle occasion de transformation
 Dans une ambiance parfois morose, il est bon de porter son regard vers des horizons prometteurs et positifs. L’année 2014 a impulsé la French Tech, un étendard derrière lequel tout entrepreneur approchant de près ou de loin le numérique, la techno, le hype ou un truc tendance pourrait se rallier. L’objectif de la French Tech est de porter nos startup françaises et les faire briller internationalement, de bien user de nos investissement de recherche et de labelliser des territoires qui participeraient activement à cette vague technologique. L’effet secondaire de cet effort, est une fédération locale, chaque territoire mettant en avant ses plus belles pépites d’innovation. Il plane ainsi un vent d’union et de collaboratif dans chaque région (un peu de compétition, aussi, mais c’est de bonne guerre). Aujourd’hui 9 métropoles sont labellisées. Axelle Lemaire et Emmanuel Macron, chargés des questions numériques et numérique, s’en sont félicités hier au cours des voeux 2015 de la French Tech. D’autres métropoles rejoindront le podium. Le cercle vertueux est lancé. Néanmoins, ce qui doit maintenant nous soucier, est de créer un vrai tissu local, d’échange de compétence, d’entrelacement des réseaux, car on le sait, l’innovation vient aussi du mélange des genres.
Dans une ambiance parfois morose, il est bon de porter son regard vers des horizons prometteurs et positifs. L’année 2014 a impulsé la French Tech, un étendard derrière lequel tout entrepreneur approchant de près ou de loin le numérique, la techno, le hype ou un truc tendance pourrait se rallier. L’objectif de la French Tech est de porter nos startup françaises et les faire briller internationalement, de bien user de nos investissement de recherche et de labelliser des territoires qui participeraient activement à cette vague technologique. L’effet secondaire de cet effort, est une fédération locale, chaque territoire mettant en avant ses plus belles pépites d’innovation. Il plane ainsi un vent d’union et de collaboratif dans chaque région (un peu de compétition, aussi, mais c’est de bonne guerre). Aujourd’hui 9 métropoles sont labellisées. Axelle Lemaire et Emmanuel Macron, chargés des questions numériques et numérique, s’en sont félicités hier au cours des voeux 2015 de la French Tech. D’autres métropoles rejoindront le podium. Le cercle vertueux est lancé. Néanmoins, ce qui doit maintenant nous soucier, est de créer un vrai tissu local, d’échange de compétence, d’entrelacement des réseaux, car on le sait, l’innovation vient aussi du mélange des genres.
Avec quelques amis du Sud, nous avons initié ce mélange, entre petits et grands, au cours d’un apéro #LittleFrenchTech réunissant les acteurs dynamiques de Marseille, Aix, Toulon, Nice, Montpellier. Avec 220 personnes, une bonne ambiance, on y croisait des startupeurs, des développeurs mobile, des consultants, des institutionnels, des VC, des mentors… C’était un beau moment de partage et d’échange entre nos talents locaux. A refaire, dupliquer et répéter, si nous souhaitons collectivement transformer cet effet French Tech.
Note : picture by Virginie G “Tatoo #LittleFrenchTech”
150 days with W3C Advisory Board
It has been few months that I have been with the W3C AB. Me and my co-advisors have met 3 times face to face, and had monthly calls to address topics related to W3C governance and strategy.
What are we supposed to discuss ? Any topic that any W3C members representative would raise, but also, anything AB believe would be helpful to deal with, in order to consolidate a strategy. While the AB meeting minutes are for W3C members only, one should note that most of the activity is held in public. That is why I encourage any curious to have a look at the W3C AB public wiki.
What is under the spot ? In the recent weeks, AB members have been negotiating what would be their main priorities in the coming year. We collected several ideas, and ranked them, based on the relevance, and the energy each of us would be ready to put on it. We came with a list of 10 projects. And I would like to emphasis here some of them that would be of interest for any W3C member and non-member.
My fav one project. Designing a long term W3C strategy. Discussion will be around finding the main area of development, where W3C should invest in order to serve its different communities. This project is detailed on a public wiki and activity can be followed on the public mailing list on whihc anyone can subscribe.
My fav’ two project (so fav that I am leading it). Making sure we keep coordination across W3C communities. the rapid development of the open web platform feature, addressing different markets, causes multiple and parallel design of new technology. this project will make sure that the synchronization is kept across the different stake holders, from W3C staff to chairs and editors. It deals with communication, process and fluid knowledge. Public wiki and public mailing list are available. Our next call will be on the 1st of December at 16:00 UTC.
My fav’ three. W3C is facing a lots of creative, multiple and constant requests for new use cases, features, improvement. And on the other hand, W3C has to maintain the existing technology. Would it be possible to detect among the new coming topic, and among the maintained topic, the ones not destinated to success ? The ones that we should stop, in order to refocus W3C forces on on high priority topics. That project is documented on that wiki.
Some other remarkable initiatives. Not all the interesting stuff to make W3C better are done in Advisory Board. Recently I have noticed two remarkable initiatives.
1) a mailing list to track any W3C working group or interest group creation http://lists.w3.org/Archives/Public/public-new-work/
2) a mailing for working groups to request reviews on their specifications http://lists.w3.org/Archives/Public/public-review-announce/2014Nov/
A very good news. Some of you might have followed that W3C was working on a mean to better regroup web developers community. The good news is that W3C has endorsed the principle to have a web developer program, based on a minimum subscription, web dev will be able to demonstrate their W3C affiliation (or at least support). First details of the plan can be found under http://www.w3.org/2014/11/Webizen.html, or you may follow @W3C_Webizen Twitter account.
Obviously if you have any idea for improving W3C working methods, environment and process, feel free to post your ideas on the public mailing list public-w3process@w3.org (archives) or contact me on @poupita !
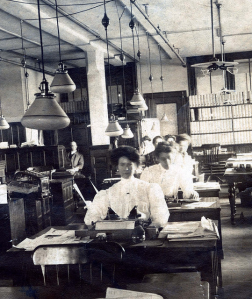
Note : picture “historic women at work” by Christine Myaskovsky
More women in W3C, and why not in W3C TAG ?
The W3C is a nice place to be. It warmly welcomes all web developers from all around the world and all companies involved in web planet and business. That is an interesting statement which is true in general. Nevertheless, this place still need to make effort in terms of diversity. International representation, small business representation, equal gender representation… The good news is that there is a coming election, which might be the right time to have minorities jumping in. The W3C Technical Architecture Group is renewing 5 seats out of 9 seats. This working group is made of participants, elected by W3C members. Its mission is to maintain the technical consistency of the open web platform. A nice mission, right ? That would fit to any good architect of the web, man or woman, I guess. How do elections work ? W3C TAG candidates are nominated by W3C members. Then among the nominated people, the W3C members will choose 5 of them.
The reason why I am advertising that election, is that I believe that more women should join the W3C TAG. Just like anyone should. But my voice here, is more to say “listen, girls, you may not realize it, but you may fit the job”.
So if you are working for a company being a W3C member, or not. And if you feel that your skills and experience will be valuable for better shaping the web. And if you would like to be part of a great team, at least, made of Daniel Appelquist (@torgo, from Telefónica), David Herman (@littlecalculist from Mozilla Foundation), Tim Berners Lee (@timberners_lee from W3C) and Peter Linss (@plinss from HP). Don’t think twice, contact your W3C representative to be nominated or look for people in you network that could nominate you. This W3C representative will have to answer the Call for Nomination here https://www.w3.org/2002/09/wbs/33280/tag-201411/ and will give you a chance to run for the W3C TAG election.
Few days left to run for that election. The deadline for being nominated is 23:59, Boston time on 30 November 2014. Go girls !
About girls, tech and innovation
 Last week, I visited The Familly offices in Paris for the Ladies Pitch Night, organized in collaboration with Girls In Tech Paris @GITParis. The pitch exercise is something that has always been attractive to me, combining the effort of form and content, with emphasis on acting and innovation, two of my favorite topics. Not to mention that girls in tech is also an important society topic for me, that event was just tailor made for me.
Last week, I visited The Familly offices in Paris for the Ladies Pitch Night, organized in collaboration with Girls In Tech Paris @GITParis. The pitch exercise is something that has always been attractive to me, combining the effort of form and content, with emphasis on acting and innovation, two of my favorite topics. Not to mention that girls in tech is also an important society topic for me, that event was just tailor made for me.
–
What is GIT ? Before listening to the candidates, we had a chance to realize how GIT network was powerful. The founder of GIT, Adrianna Gascoigne @afgascoigne, came on stage to remind us the rationale that lead to the creation of Girls In Tech @GirlsinTech. Her story which started in 2007 was nice, it was about making the technical and entrepreneur world more keen to welcome girls, and she used her energy to create a program focusing on girls education, engagement, solidarity, friendship and fun. That nice story was similar for most of the other female speakers supporting that event, on stage Joanna Shields @joannashields, Digital Advisor to the Prime Minister of the UK, on the video with kind messages to the ladies : Nellie Kroes VP of the European Commission, leading the digital agenda @NeelieKroes, and Sheryl Sandberg from Facebook @sherylsandberg. Last but not least, Roxanne Varza @roxannevarza was representing Girls In Tech Paris, together with @moumsinette @audreysoussan @sjerusalmy @nicolasmagand @marionnougier. The french governement was supposed to be represented by Axelle Lemaire, but regrets were duly sent.
I miss you 2! Good luck! #lpn2014 @GITParis #womenpower
— Axelle Lemaire (@axellelemaire) September 23, 2014
To complete the demonstration that Girls In Tech had a worldwide coverage, kind messages from some of the 42 GIT chapters all around the world were shared. It happened that some of them were represented, among the 200 attendees , together with some funding companies, some girls in tech, some boys in tech, and a lots of enthusiastic people. Yes, the nice and large The Familly lounge, located under a glass dome, was fully packed! All got the message that a study related to female entrepreneurship demonstrated that women, when setting up a business and making money, are superior in the following area, compared to male entrepreneurship : investing in education and familly, innovating, and job creation, thus creating more wealth. I felt strange that this business argument had to be stated clearly, and that emphasis on gender equity was not mentioned, but this evening was about innovative economy.
Then, the startup pitch. Five girls went on stage to pitch, in front of a jury made of prestigious people.
#lpn2014 @GITParis brings the best of the #Tech World to #Paris tonight w/@mikebutcher @BrendaOConnell @LatoucheP @elianefiolet @rsohoni — Frédéric Hermelin (@FredHermelin) September 23, 2014
The pitches were 6 minutes long – which actually made them long enough to allow the audience to get the style and character of each presenter. Most of them were following the fil rouge ‘I wanna a tell you something personnal, i/we/she/the world has a problem, here is how to solve it, here is the way I’ll make money out of it, look at our nice team, thanks I love you’, the all with nice slides. Well, a standard pitch.
Easy size, Cocofarm, Cortechs, Fojo and Gemmyo! Great european start up in this event! #LPN2014 — Estelle L-A (@Madinelle) September 23, 2014
Easy Size @EasySize. The system allowing online clothes shops to make life easier to customers. When ordering a trouser, no need anymore to give your size, to measure the length of your leg or the tour de taille. You just indicate another item (from any brand) that you have already bought and worn with success, and the prediction algorithm will calculate the translation into the item you are willing to buy. 79 % of the predictions are correct. See more http://www.easysize.me/
Cocofarm. An application allowing farmers to manage their eggs and follow their production and productivity. The energy of the lady pitching impressed all people, specially when she cracked an egg on the floor… That little business target seems to be just a beginning for that startup, willing to make life easier to country side small businesses.
Cortechs @cortechs_ab. That solution aims to help kids with light mental disorder related to concentration. It requires an headset, to measure brain activity of the patient, together with an application offering games. Objectibe being here to bring back patient into a focused and quite mood. That presentation while looking like a research topic was really intereting and demonstrated some real business potential. See more here http://cortechs.ie/
Fojo.me. A mobile application, allowing to take picture (sounds regular), make some nice effects on it (looks normal) and develop with your vintage old dark room. Yes, the idea is to ntegrate your mobile phone into the process of the actual picture development. Niche market, but a smart way to bring back digital photos into paper pictures on your wall. See more here : http://fojo.me/
Gemmyo @gemmyoParis. A online shop, where jewels can be ordered, and will be 3D printed, at a price which will make luxury jewellery affordable. Well, that’s the promise. You will find the same quality, similar design, but will avoid the sometime uncomfortable situation where you just dont believe the little ring you want to buy is soo expensive. More here : https://www.gemmyo.com/
Five girls, five characters, five positioning, five countries. The jury rewarded EasySize startup, and everyone went to the nice buffet. One should anyway keep from that event that girls are not special entrepreneur, they have great ideas, impressive willpower, but they found here an amazing network to put them on good tracks !
Keep track of it, by supporting Girls In Tech whatever your town or country ! GIT Paris or GIT everywhere.
French local note: girls from Marseille, please be aware that Girls in Tech Marseille has now an ambassador
Très fière d’être la représentante de GIT Marseille. Bienvenue à toutes/tous dans le sud. #lpn14 @MarionNougier @afgascoigne @roxannevarza
— laurence bricteux (@laurence0501) September 23, 2014
W3C Web Crypto, what’s next ?
 Where is Web Crypto ?
Where is Web Crypto ?
For the ones wondering if the Web Crypto is a dead topic in W3C, they should not worry anymore. The Web Crypto API is safe. It is still trying to define the primitives of cryptographic operations, to be integrated in all browsers, and it is still alive. What we mean by alive in W3C is that : it entered Last Call, and received a serious amount of great feedbacks, from smart reviewers and this is the good sign of interest. The dark side of having productive reviews is that it takes time to address all of them. That is why you have not heard about W3C Web Crypto API since the summer : editors Ryan Sleevi from Google and Mark Watson from Netflix are busy, with the Working Group to solve open bugs (see our bugzilla repository).
Yes, some bugs are more complex then others…
At the moment the Working Group is reviewing interesting items :
– Making sure the specification is extensible to integrate new algorithms or new type of algorithms (see related bug)
– Trying to find a way to include specific algorithms such as NUMS curves and 25519 curve (see related bug). That discussion is obviously related to the idea of specification extensibility. But those candidates are special in a way that some related discussions are happening in IETF. IETF is currently discussing the set of algorithms that will be recomended for next TLS version. We know that several candidates are running, and IETF and W3C should on that matter stay synchronized, nevertheless the sensitive aspect is that IETF is not scheduled to make decision before its next meeting, in early November.
Once those bugs will be resolved, with few other ones, we might be in a position to exit Last Call, lets say in September. This means that we could start moving toward Proposed Recommendation. Another great adventure…
Proposed Recommendation ? What does it mean ?
It means that W3C is calling for implementations, experiments, based on the specification as edited in its Last Call exit. That specification may embedd some feature at risk. Meaning some features that my be dropped after implementations demonstrated it is not reasonnable, technically viable or feasible. But this is where we will see implementations happening. The implementers will have to demonstrate their interoperability, that is why we will develop tests (note that a repository is already existing, we just need to fill it with smart and relevant tests). Several implementations have been referenced already in Chromium (see related issue), in Firefox (see related bugzilla) and pending in WebKit (see related bugzilla) and Internet Explorer (see IE11 preview announcement).
Those beginning of implementations on the browser side make that specification on good track to become an actual W3C recommendation, with associated prooducts. This should happen, lets say… in 2015 (standards are living in a timezone where milestones are barely predictive, but are supposed to follow a process, see W3C one)
Do we close the Working Group, after that ?
During the last 2 years, the Web Crypto WG has been addressing a variety of problem and features, some of them have been parked. That is why even if being in Last Call for the Web Crypto API, the working is already thinking about its next version. The discussion about prioritization of next web crypto API will happen during a 2 days workshop, held in Mountain View on the 10 and 11th of September. Two days for that topic may sound long, but it appears that the topic of cryptographic is also related to other key aspects such as usage of secure token, like hardware or trusted software are, or web authentication operation – where FIDO Alliance is currently working on, or again certificate management and in general linked to browser security. Gathering all actors having some interests in that topic will hopefully help W3C to identify realistic features to be added in the open web platform. The workshop will be quite crowded as 70 people coming from 47 companies, all discussions will be accurately minuted and a report will be issued. You may hear about it on that same blog…
Note : you can also read more about the Web Crypto API scope by reading an old post here : https://poulpita.com/2013/07/31/first-web-crypto-implementations-expecting-your-imagination-to-play-with/
[RMLL2014] Free software, thinker, geeks, all in one place
Let me get you jealous of me… Summer time. South of France. Ideal conditions to attend the worldwide conference of the free software (Rencontres Mondiales du Logiciel Libre, in french). Lets call it RMLL2014. What is it about ? All about free software and open source, covering broad topics such as society, internet, art, collaborative tools, software suites, security, open data…
All free software, offering alternatives to proprietary software, together with its designer, coders, evangelist and their free mindset were present. One may ask ‘what the hell was she doing there ?’. That happened because Christophe Brocas @cbrocas, Mathieu Blanc @moutane, and Philippe Teuwen @doegox organized a security track. And it happens that free software, open source, W3C security do have something in common. My presence here, was also the opportunity to attend some amazing talks. Here are some benefit of sitting here and listen.
Getting free software essence, from Richard Stallman, himself
Mister Free Software Foundation, the daddy of GNUproject, the man who showed the path to open source, collaborative wealth and promoting citizen control over software. After selling few goodies for the FSF and taking pictures with fan, Richard Matthew Stallman exposed his theory. Simple and efficient. Any software which is not open is killing freedom and is a potential danger. As a consequence, a relevant software has to embed the following merits : the freedom to run the program as you wish, for any purpose (freedom 0), to study how the program works, and adapt it to your needs (freedom 1), to redistribute copies so you can help your neighbor (freedom 2), to improve the program, and release your improvements to the public, so that the whole community benefits (freedom 3). This implies access to the software source code. The ideology behind that business model proposal is to give back power to the people, reducing technology attacks on citizen freedom. Having by default the possibility to analyse collectively a software gives, from Stallman perspectives, more chance to refrain editors to performed actions without user consent (understand, implementing tempting things such as backdoors, user tracking systems…).
Discovering Caliopen, the new private messaging project, by Laurent Chemla
Another free thinker. Laurent Chemla, french, on the internet since ages, promoter of individual freedom and collective activism, founder of Gandi (a hosting server service). Laurent wrote ‘Confession d’un voleur‘ (confession of a robbery) in 2002, where he confesses how he made money because he was curious and visionary, because playing days at nigh on internet while other did not realize it was existing. This gave him a competitive advantage he transformed into money, but he did not feel comfortable with it, as his vision was more that internet was about changing the world, and giving a chance for the citizen to take power back on politics and locked systems. Since few months, Laurent is working and thinking about a new service related to messaging, that would fit his dream, aka being privacy centric and secured. Rationale for designing this offer is the following : freedom is at risk those days (and since a long time, by the way, but lets pretend Snowden was a new thing, says Laurent). Except few geeks ready to get technical skills to protect themselves and suffer the pain of using PGP, noone is really taking serious action. He re-assessed that freedom must be protected, by political and social actions, but also with technical tools (another domain where he feels he can do something). Laurent does not want to build another complex solution, or a like-gmail-but-more-secured solution, but rather offer to users an attractive email service. Here is Caliopen. Caliopen promise is to manage conversation, whatever is their media (email, sms, pigeon, …) and associate trust level to every piece of the communication. A user, a conversation, a device, a context for using Caliopen, any central piece has a trusting level. Which allows power to the user to decide. Shall I send this sensitive email to my friend Stéphanie who is well known for opening her mails on her crappy device in the train, on public wifi ? Part of Caliopen exists, the back end side, and the project is looking for skilly web developers to code the client side.
Hearing recent news about Tor Project, by Lunar
Lunar is one of the voice of the french association Nos Oignons, which aims to raise fund and maintain some exit nodes of Tor project. Lunar shared during the security Track of the RMLL2014 principles, weaknesses, and stakes behind Tor Project. For the ones not yet familiar with Tor, it is a network allowing users to access to internet resource, with an anonymized address. The aim is to counter the filters over internet imposed by application, services, ISP or government. Tor Project relies on a network of 4000 nodes, which are driving the communication on a random path, inducing the scrambling of the IP address of the machine which initiated the request. lunar is clear. Anonymity is not perfect. For example by spying data entering the Tor network, and data getting out of the network and making correlation. For example, some information about traffic can be guessed by observing the Tor Network life, or by entering the guard allocation entry and exit nodes… But the network is used and maintained by people having a vision, always trying to improve its reliability, usability, supported by a researcher community. What was also discussed were the conditions for hosting an exit node. As it is a special node, exposed to a large traffic, and to potential legal attacks, it requires to have a fix IP address, with reception of notification and better if it is an association behind, rather then a specific person. Integration of Tor access into software is also a key discussion point and the conclusion was that only Tor Browser or Tails should be used. One should note that Mozilla and Tor Project are working together on the definition of the next privacy feature of Firefox, in order to make ‘private navigation’ a feature with a real value proposition. Lets stay tuned… A lots of usefull references for understanding Tor projects and limits can be found under https://pad.riseup.net/p/lsm2014-tor.
Next episod of that post will tell you more about other projects discussed in the RMLL2014 Security track…