In december, I was in a web conference, named #BlendWebMix, which gathers all kind of actors of the web economy, from investors to tech, including designers, influencers, politics, startupers, … Very diverse type of talks were given, 80, and 1800 people attended the event. I was selected to give a very short presentation on privacy and security. My challenge was : convincing a broad audience that the privacy was something each of us, as workers, should take action for, in 13 minutes. Here is the core of my message.
I am fed up with the usual talk in security which says ‘provide privacy by implementing some security or you will burn in the hell of bad reputation companies, together with Madison, Target, Yahoo, and potentially bankrupts”. You know, that Fear Uncertainty and Doubt (FUD). I tried another angle. I tried the non-violent path. And I believe there are at least two good reasons why people should give a chance (and budget and effort) to the privacy.
The first reason can be found on the optimistic side of the life. The good reputation. I have the feeling that in this digital storm of hacks, global attacks, social media bashing, the companies taking action to preserve the privacy of the users are playing a good game. And the user may know. And the user may appreciate it. And it may be a competitive advantage to invest and get rewarded for it.

The second reason is the data protection, as defined by the european comission. There is a new directive that mandates every company to allow its user to keep an eye on their data. It is the result of long discussions related to the value of the citizen privacy in our digital world. That regulation will be applicable in May 2018, to all European companies or all non-european companies handling some European citizen data. Well, yes, 2018 is after tomorrow. Which gives you only tomorrow to ramp up in good practices and get ready. The threat; if you are not compliant with the regulation, will directly touch your wallet, as fees could go up to 4% of your benefits, as a company. Universities and public services are also submitted to this regulation.
What does this regulation say ? It says that users will have to explicitly opt-in for registering their data, they will be able to control what you are doing with the data, they will have the right to modify and delete their data. In addition the data portability will have to be provided. Finally, users will have to be informed about any breach related to their data. Data in this context, means any piece of information which characterized the user, name, address, but also geo-localisation, social media activity, any digital evidence left by the user that you are collecting.
Who is submitted to this regulation ? Any company which collects, processes, transmits, stores the data. This means, you, but also anyone touching the data closely or by far. For example, the monetization partners (ads), or your cloud providers. Now you see what could be the impact !
Duing the talk, I started a new technic for getting the audience sensitive to the message. I asked them to pause a second, to close their eyes, to breathe, and think about one of their user. Lea, 30 years old, digital, agile, conscious citizen, caring about her privacy. I asked the audience to answer in the secret of their mind and heart, eyes still closed, the following questions : do you know what are the data from Lea that you are taking in your super-super application or service ? Do you know where are Lea’s data stored ? When was the last time you had a conversation about privacy and security at work ? I mean, not on Twitter, being scandalized by the global surveillance of the states, but wondering, in your own framework. Some of the people in the audience smiled, and I felt some of the questions touched of them. What about you ?.
Targeting to convince the audience in a smooth way to take action for the privacy of their users. I reminded that it was important for them to identify the data, understand their life cycle in their own service life cycle, define some weak points (aka, any entry point, transfert, storage…) and protect those points. The thing is that of you are a small company, you may not know where to start. My key message was. Well. Start with pragmatic stuff.
First. Talk about security, create conversation around it. For example. Make a 2 hours meeting with the project manager or whoever in the company coded the solution, with a global view. And together make a status of the different security measures done up to know. Make an accurate status.
Second. Look for security champion(s) in your team. Basically the one(s) who had a security training at school or who had the chance to work on a security sensitive project in the past and may share with others.
Third. Write a process. It could be a paper sheet on the cafeteria reminding, i) before you ship a new feature, ask John (the security champion) to have a code review, ii) before you sign a deal with a company, check its track record in security, …. Or it could be a professional methodology for bigger companies. Well, the objective is just to make sure that the question of the security is handled in the product life cycle, at company scale, and taken into account in the delays and deals. This relates to create a security company culture.
Fourth. Engage conversation with your partners, providers, ask them the basic question on their security investment. They might be able to prove that they actually take care of it. With certification, or being able to tell you a nice story about their effort in that matter. Just like any company should be prepared to.
Fifth. Crash test your product. Some bug bounties platform are now existing. You can submit your product, it will be attacked by some hackers, and if some security vulnerabilities are found, you will be informed. The next level or complementary action could be to perform an audit of your code, or have actual security certification (but I guess that if you are on a market where security certification scheme exists, you might already be a security aware company).
Sixth. Have a monitoring of the security news. Read some newspapers specialize din sec, or some forum alerting on vulnerabilities. It would be a pity if your service bim-bam-boum were based on a framework which has been seriously hacked, and that you are not aware of.
In the end. Six possible concrete actions. To be rolled out by any non-expert security. I asked again the audience to close their eyes. And to pick in that list one action, just one action. And promise, in the secret of their mind to do it, Monday morning, when coming back in the office.Hoping next Monday some SMB will enter the way of improving privacy of their services….
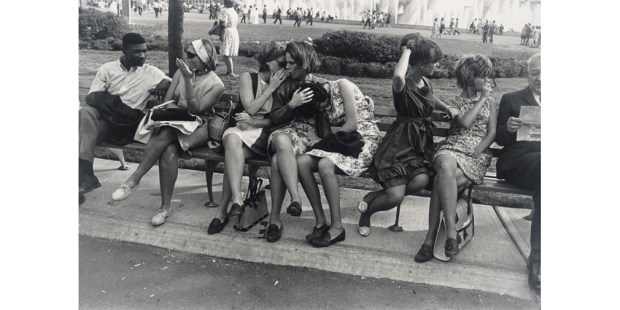
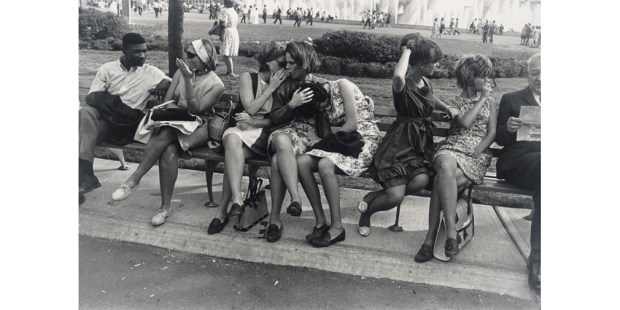
Note : all picture copyrighted Garry Winogrand